Logo Detection with OpenCV
For a few years, I've wanted to play with OpenCV for logo detection, but never got around to it. However, now that I've started using Copilot, it's lowered the activation energy for new projects, and I was pleasantly surprised by the results.
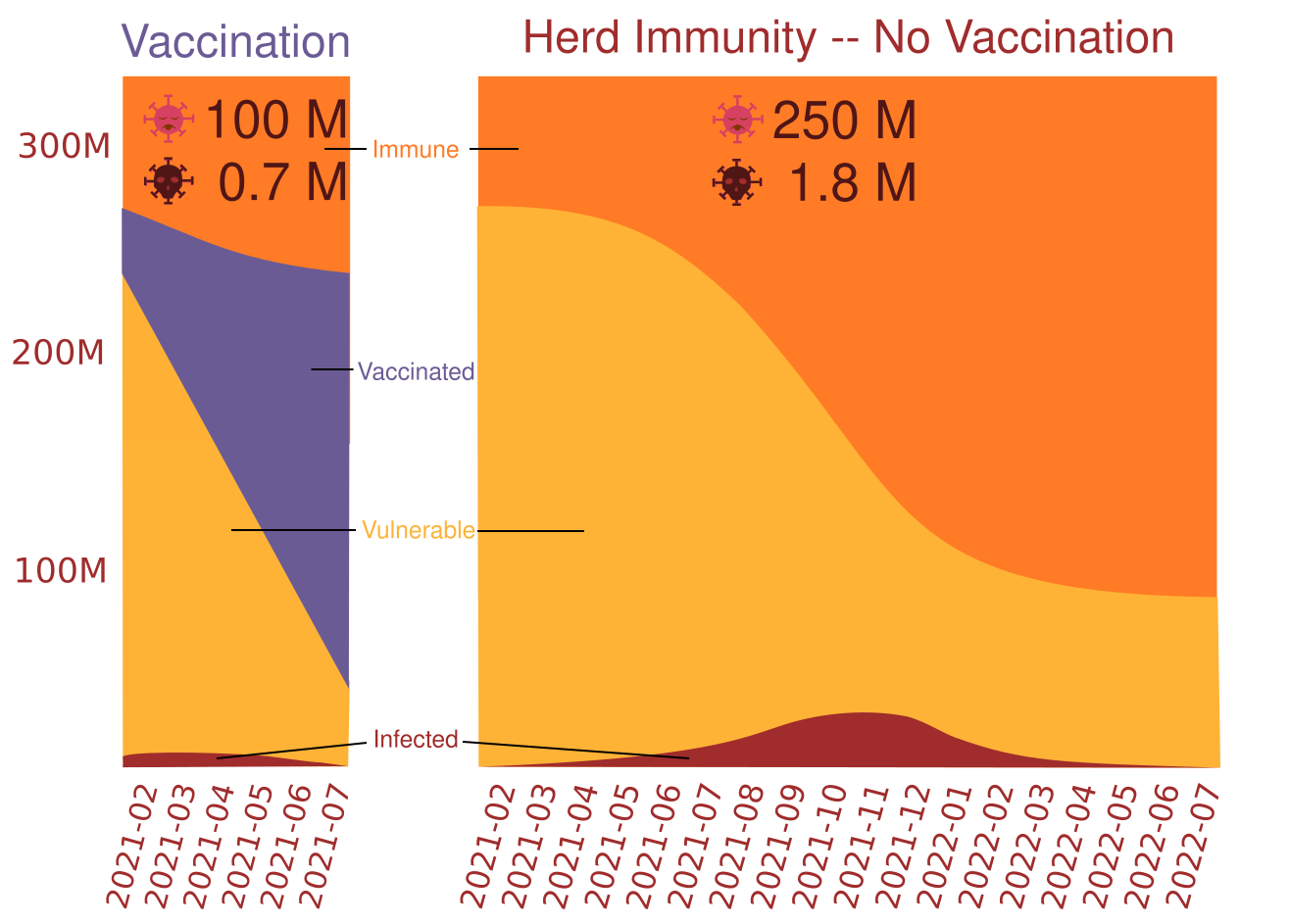
Simulation - Covid Vaccine Impact
Modeling the implications of vaccine distribution can be daunting, but, with a few basic assumptions, it becomes possible to create a simulation that can be used to run experiments on how various actions might impact the course of the pandemic.
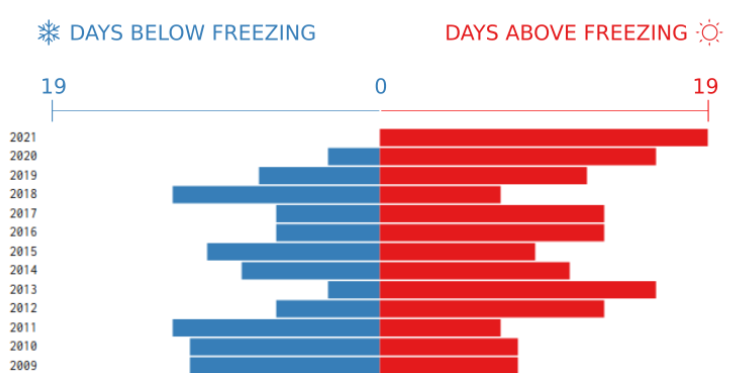
Visualization - An Unusually Mild NYC January
Over the past weekend, I was happy the weather was warm enough to enjoy spending some time outside, but it started me thinking... it's been pretty warm this year... is this unusual? As it turns out, there hasn't been a single day where the average temperature was below freezing so far this year in NYC. Surely this must happen from time to time. I decided to check the historical data for every year starting from 1949 for the period of January 1st - 19th ... lo and behold, it has never happened in the entire data set until this year!
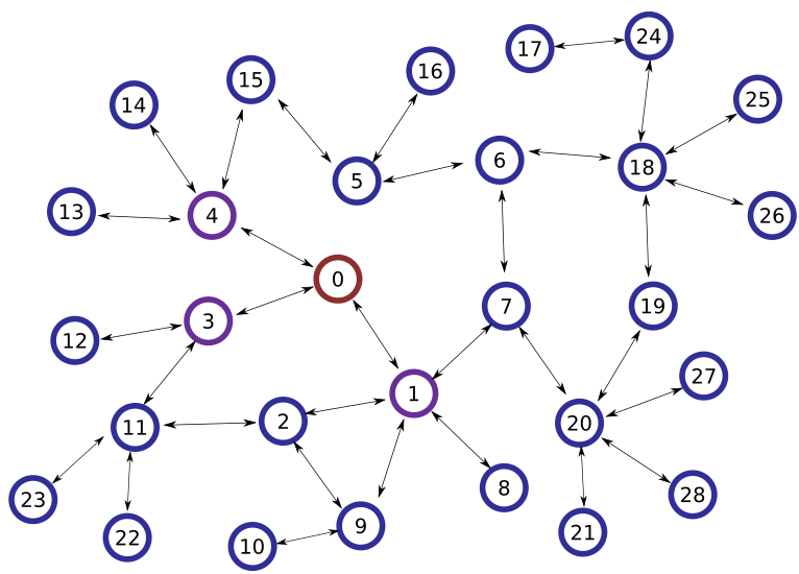
Contact Tracing Example
Contact tracing with isolation can be an effective way to stop or slow the spread of an outbreak. In this post, we'll examine a method for determining potentially infected contacts based on a provided trace.
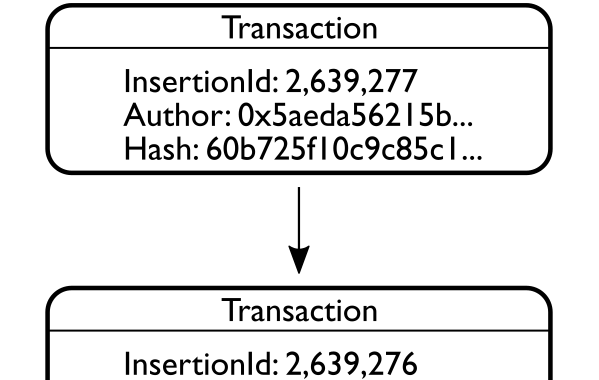
Ethereum Blockchain Tutorial - SmartContracts
SmartContracts may be the most revolutionary application blockchain technology has enabled. SmartContracts allow for the creation of trustless verifiable agreements that can be enforced by the network. Because the rules that govern contract execution are written in code rather than human language, no judge or abitrator is required to enforce the contract. Code is law, and, for better or for worse, once a SmartContract is agreed to, it is forever binding.
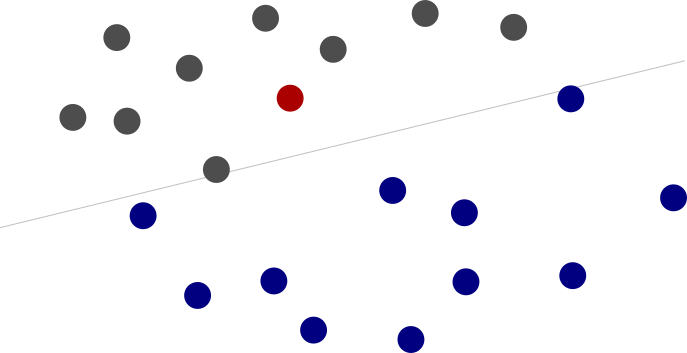
Machine Learning Tutorial - Random Learning
The key to understanding machine learning is to break it down to first principles. At its core, machine learning is about automatically making, updating, and validating predictions. While there are many elegant ways to accomplish this, it is helpful to start with a simplified model and build from there.
How Memory Impacts Decision Making
Q-learning is a reinforcement learning technique that provides a model of how agents use memory to make decisions. In my implementation, the agent finds the optimal policy for a Markov decision process by transitioning to the state with the highest expected value.
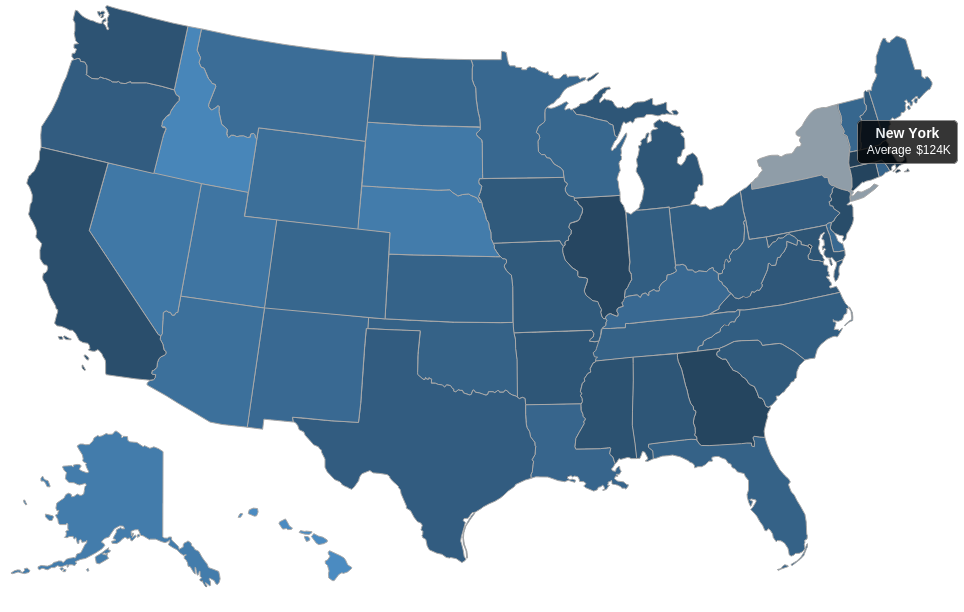
Visualizing Developer Income by State with D3
The average salary for developers varies widely across the United States from $129K/year in DC to $63K/year in Hawaii according to salary data from Indeed. Using D3 to create a choropleth map, we can quickly see which states have the most lucrartive tech opportunites.
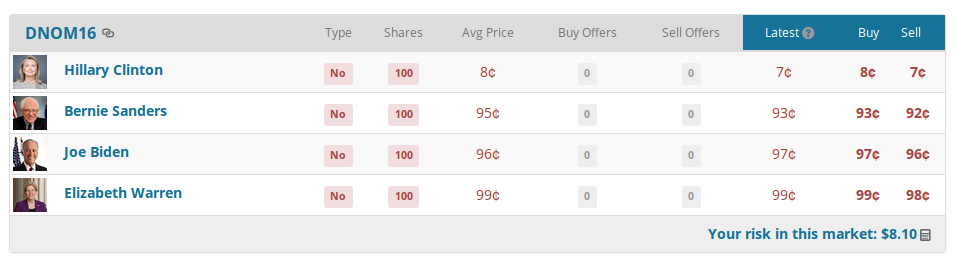
Examining Prediction Market Anomalies
Market inefficiencies can be difficult to identify and are usually competed away quickly but, prediction market trading restrictions can cause anomalies to occur frequently.
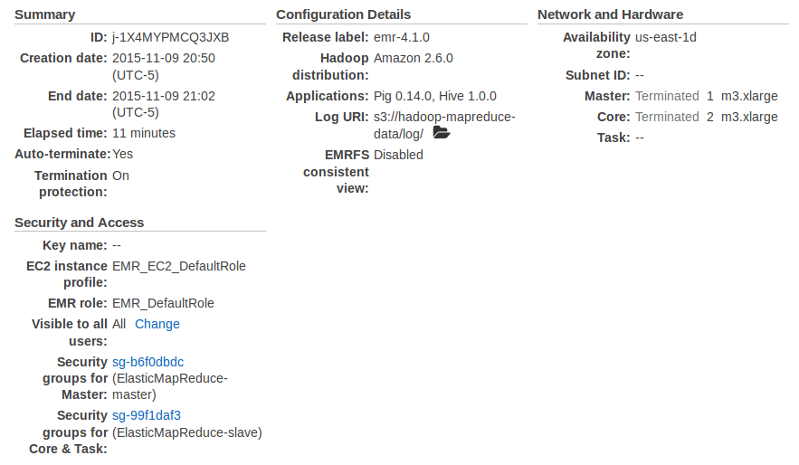
Processing Big Data with Elastic MapReduce
A few years ago, setting up a Hadoop cluster was a painstaking challenge, especially with ever shifting dependencies and documentation that was usually not quite up-to-date. Today things are easier, but, even now, setting up a cluster is no small task. Recently, however, I ran some experiments with Amazon's Elastic MapReduce (EMR) and the entire process was swift and painless.
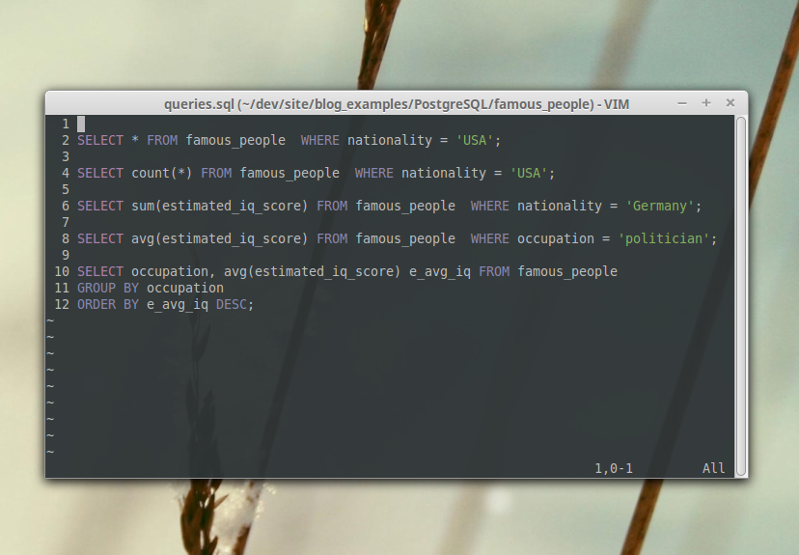
Basic Querying with PostgreSQL
In the previous post, we looked at data normalization in PostgreSQL. In this tutorial, we'll expand on our work to write queries that answer questions about the data.
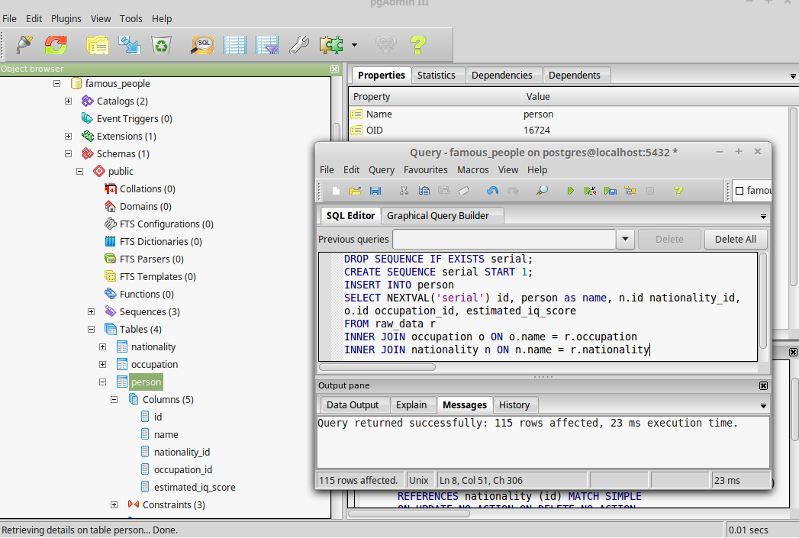
Data Wrangling with PostgreSQL
Wrangling raw data into well normalized, efficiently queryable tables in PostgreSQL can be challenging, especially for those with limited prior SQL exposure. In this tutorial, I've created a step by step guide to walk you through the process of munging and normalizing data about famous people from a practice data set.
Visualizing Conway's Game of Life with Matplotlib
While working through practice problems on leetcode, I encountered a problem I hadn't seen for a while, Conway's Game of Life. After implementing the solution, I decided it would be interesting to take it a step further and generate graphics to display the game.
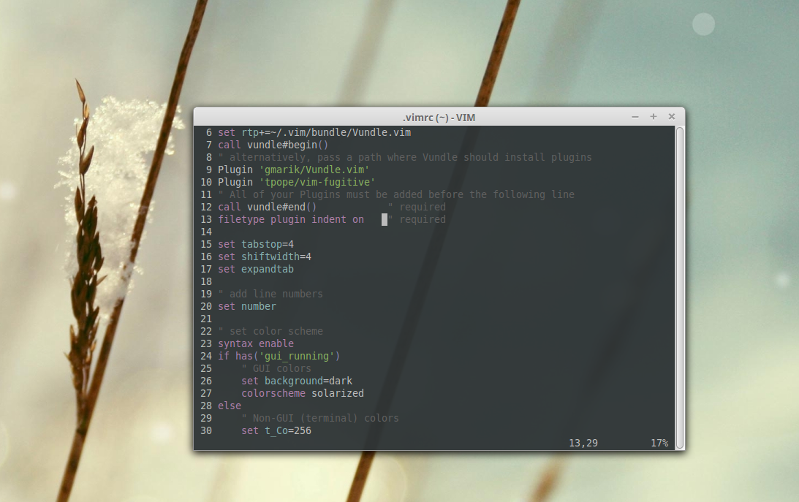
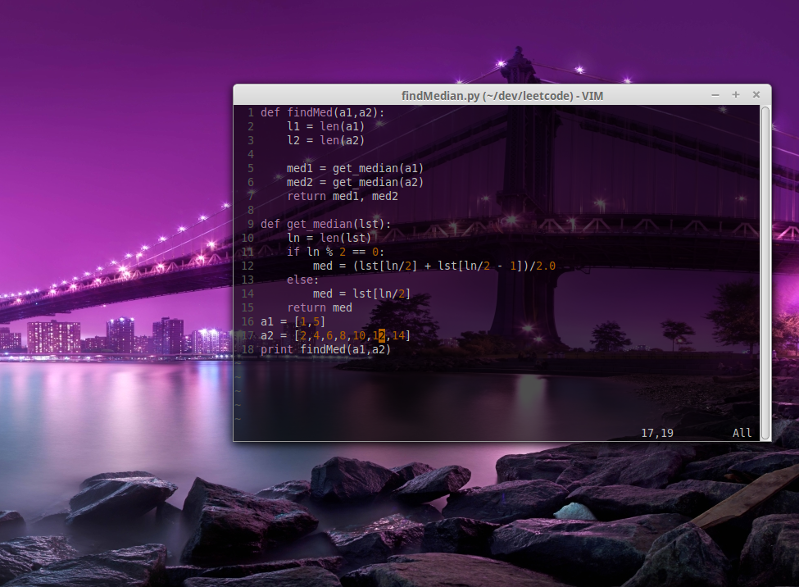
Syncing Vim Across Different Environments
One of the great things about Vim is that it requires very little customization. For the things that you do want to customize, however, it's really good when you can keep everything in sync across your various environments.
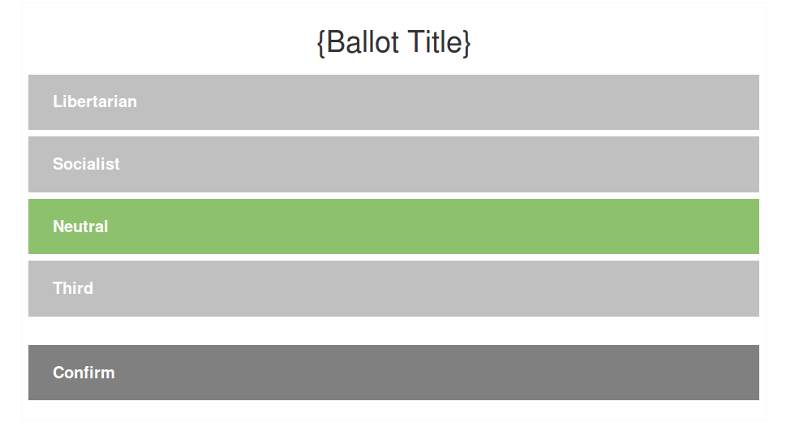
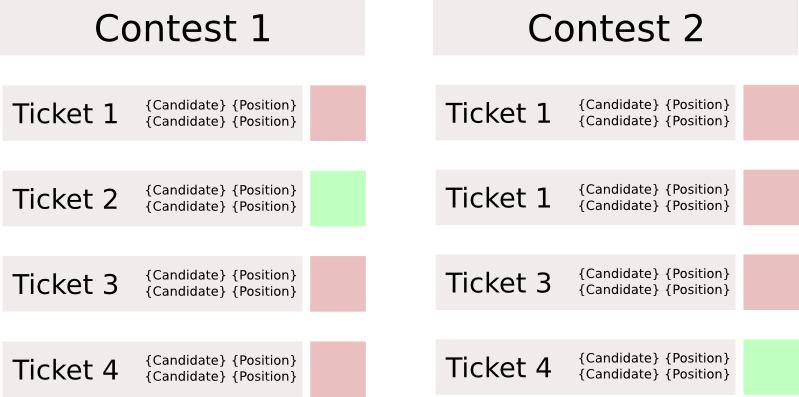
Verifiable Election System Demo
In an earlier post, we looked at the mechanics behind creating an election system where the results could be verified by any third party while still protecting voter privacy. In this post, we'll look at a demo implementation of a user interface for this system.
Spotting Malicious Code Hidden in Plain Sight
Recently, Peter Jaric hosted a Javascript misdirection contest where contestants attempted to write elegant code to surreptitiously pass a generated key to a remote server. The trick of the contest, however, was to hide the malicious code in plain sight.
Modeling Verifiable Voting that Protects Privacy
Technology has made it possible to design an election system that is both transparent and verifiable, but still protects the privacy of the ballot box.
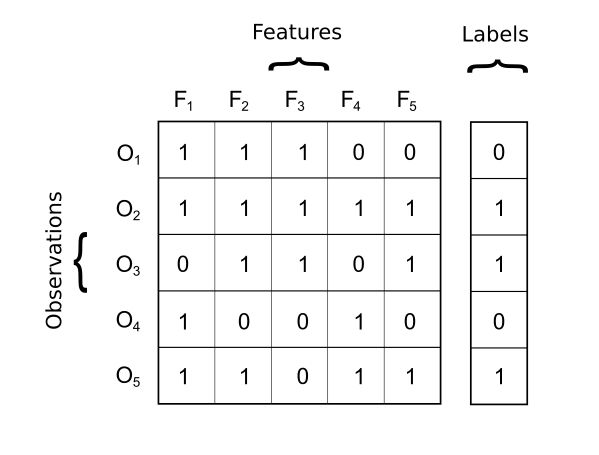
Basic Supervised Learning Overview
There are some really good tools for supervised learning out there. Every popular language has them. Most of the existing toolkits will have all of the algorithms mentioned here plus a lot more. If you're comfortable with Python, I suggest starting with scikit learn since it has a standard interface for all of its machine learning techniques.
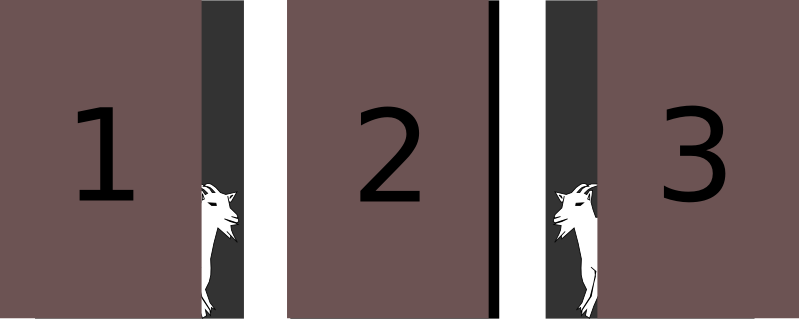
Modeling the Monty Hall Problem with Python
At first glance, the Monty Hall problem can seem counterintuitive, but, when viewed from the correct perspective, the appropriate strategy becomes abundantly apparent.
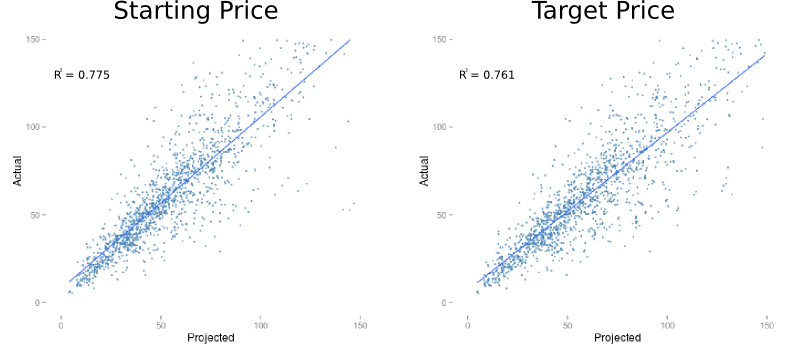
Price Targets a Poor Predictor of Performance
In order to determine the relationship between consensus price targes and stock performance, I decided to measure the accuracy of predictions made from 2013 to the first two quarters of 2014 against the actual results from the matching quarter of the following year.
Configuring Vim for Use in the Terminal
GVim is great for a local machine, but sometimes it isn't possible to use when working on a remote server. Never fear, with the right configuration, Vim can look just as great even when it is running in terminal mode.
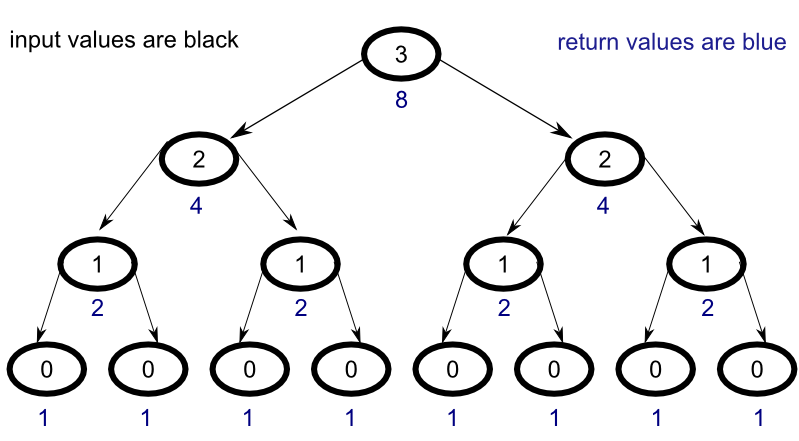
Stepping Through Memoization in Haskell
To better understand how memoization works with Haskell's lazy evaluation, let's walk through a simple example step by step. As a learning tool, we'll examine a simple function that raises the number two to a the power of whatever number is given as input.
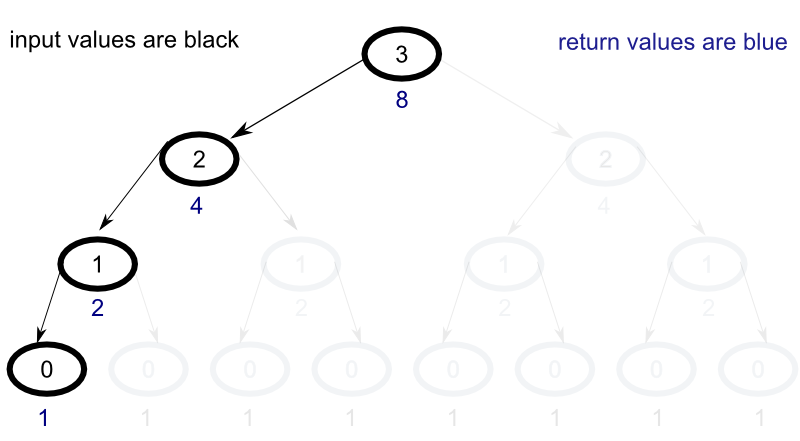
Understanding Recursion in Haskell
To understand how recursion works, let's walk through a simple example step by step. As a learning tool, we'll create a simple function that raises the number two to a the power of whatever number is given as input. Let's take a look at the implemenation to get a better idea of how the process works.